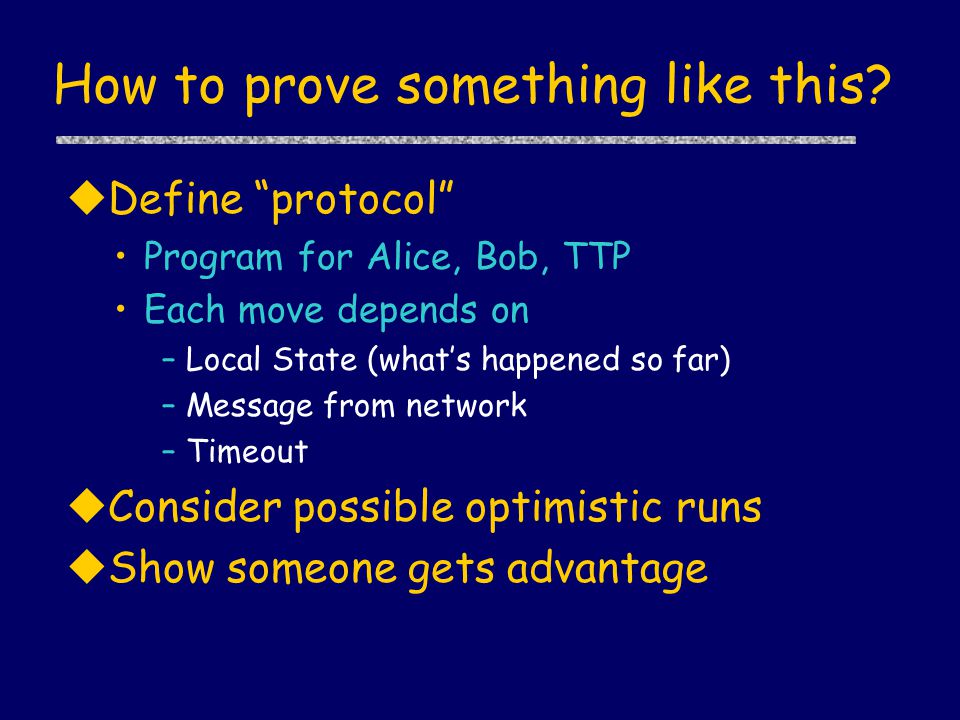
Threats to Modern Cryptography and State-of- the-Art Solutions Kenny Paterson Information Security Group. - ppt download
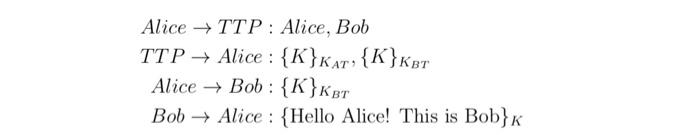
![PDF] A Hierarchical Trusted Thir d-Party System for Secure Peer-to-Peer Transactions | Semantic Scholar PDF] A Hierarchical Trusted Thir d-Party System for Secure Peer-to-Peer Transactions | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/f5e9dd671605683559b5d880d9ac04a78d3fd02b/23-Figure7-1.png)
PDF] A Hierarchical Trusted Thir d-Party System for Secure Peer-to-Peer Transactions | Semantic Scholar
![PDF] A Hierarchical Trusted Thir d-Party System for Secure Peer-to-Peer Transactions | Semantic Scholar PDF] A Hierarchical Trusted Thir d-Party System for Secure Peer-to-Peer Transactions | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/f5e9dd671605683559b5d880d9ac04a78d3fd02b/16-Table1-1.png)
PDF] A Hierarchical Trusted Thir d-Party System for Secure Peer-to-Peer Transactions | Semantic Scholar